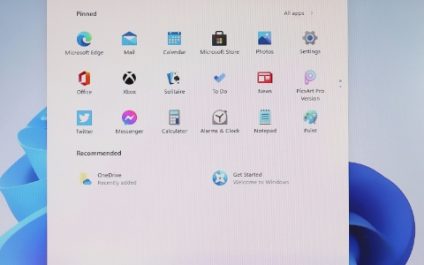
Windows comes with a plethora of default settings that aren’t to everyone’s taste and many users find extremely irritating. This guide helps you cut out many of the annoying Windows features so you can boost your productivity and bring peace back to your digital workspace. 1. The disturbing jingle of Windows widgets Gone are the […]
Learn how to fix these 7 annoying Windows features
Key tips for boosting online security

The digital landscape is riddled with threats: malware attacks, phishing scams, and data breaches are just a few. But by taking a proactive approach to cybersecurity, you can significantly reduce your risk and keep your business safe. Here’s a guide to fortifying your online defenses. Create strong, unique passwords Passwords are your first line of […]
Evaluating BYOD and CYOD policies for optimal productivity

Empowering your workforce with mobile devices can enhance productivity and flexibility. However, a key consideration is the device ownership model. This document explores BYOD (bring your own device) and CYOD (choose your own device) approaches, outlining their respective strengths and weaknesses to help you determine the optimal strategy for your organization. What is BYOD? With […]
5 Crucial VoIP security measures to protect your business

Many businesses today can’t live without Voice over Internet Protocol (VoIP) systems, which provide a wealth of features and benefits, primarily cost savings and advanced functionalities. However, with these advantages comes the risk of cyberthreats targeting VoIP infrastructures. To mitigate these risks, businesses must implement the following measures. Enhance password security Your passwords serve as […]
Unlock your team’s peak productivity with Viva Insights

Wondering how your team can get past its productivity plateau? Feeling like there’s untapped potential hidden within your workflows? Your search for answers ends with Viva Insights. This innovative tool from Microsoft uses the power of data to analyze your team’s collaboration patterns and identify areas for improvement. Here’s how you can utilize Viva Insights […]
Debunking top disaster recovery myths: Essential insights for businesses

As businesses embrace digital transformation, the specter of disasters looms larger than ever. Cyberattacks, system failures, and natural disasters are no longer rare occurrences but rather everyday challenges that organizations must confront. However, amidst these challenges, numerous myths and misconceptions about disaster recovery persist. Myth 1: Disaster recovery is only necessary for large corporations News […]
Understanding the role of cyber insurance

The evolving cyberthreat landscape poses a significant risk to small businesses. Cybercriminals often target such businesses due to the valuable data they possess and possibly less advanced security measures. To protect themselves, small businesses often implement safeguards including firewalls, data backups, and ongoing cybersecurity training for employees. However, these solutions alone may not be sufficient […]
Does unified communications impact business growth?

For many businesses today, unified communications (UC) is a game-changer. By streamlining communication processes, UC has the power to revolutionize business communication systems, resulting in reduced costs and numerous other benefits. In this article, we delve into the rising cost-efficiency and accessibility of UC solutions, highlighting their indispensable role for many companies. Unified communications defined […]
How to conquer desktop clutter in minutes

The ever-growing pile of icons and documents littering your desktop can feel like an insurmountable mountain, casting a shadow over your productivity. But did you know that conquering clutter doesn’t have to be an arduous task? In fact, with the right approach, you can reclaim control over your digital workspace in mere minutes. Read on […]
NIST-recommended guidelines for passwords

Weak passwords and bad password management habits continue to be significant cybersecurity threats, jeopardizing the integrity of critical data and systems. Recognizing this risk, the National Institute of Standards and Technology (NIST) developed standards and best practices for password creation and management. By following the NIST guidelines, users can significantly improve password strength and cybersecurity. […]